Authors: no one regularly calls a thing by its full name in informal conversation. In the real world, a television is a TV. People talk about “Smith”, not “President John Smith”. If the star Betelgeuse were a part of everyday chat, it’d be called Juice. All this is 10x true if the military’s involved. No one loves funny nicknames more than the rank and file. Some smartass would call it “Orenthal” one time, and from then it’d be compressed to “Orntall”.
I’m finally getting around to watching the WWDC keynote. Fun fact: if a presenter lowers their hands below waist level, or goes more than 3 seconds before waving them about, they’re penalized stock options.
That’s the only explanation I have for it. Every single presenter, every time. If you had a drinking game for whenever someone swings their hands wide and brings them back together, you’d be dead by the first section.
I bought a DM42n calculator a while ago and it’s been a fun desk toy that I admittedly have little practical need for. I’ve since updated it to use the C47 system which is the most delightfully nerdy, ludicrously powerful calculator mankind’s ever schemed up. My kingdom for a printed manual, but still!
The World Cup potato chip bags look like a xenomorph with an underbite. It creeps me out.

I took my wife and kid to an outdoor swap meet for a few hours around lunchtime today, and now I’m reminded that the sun hates me and wishes to smite me at every chance.
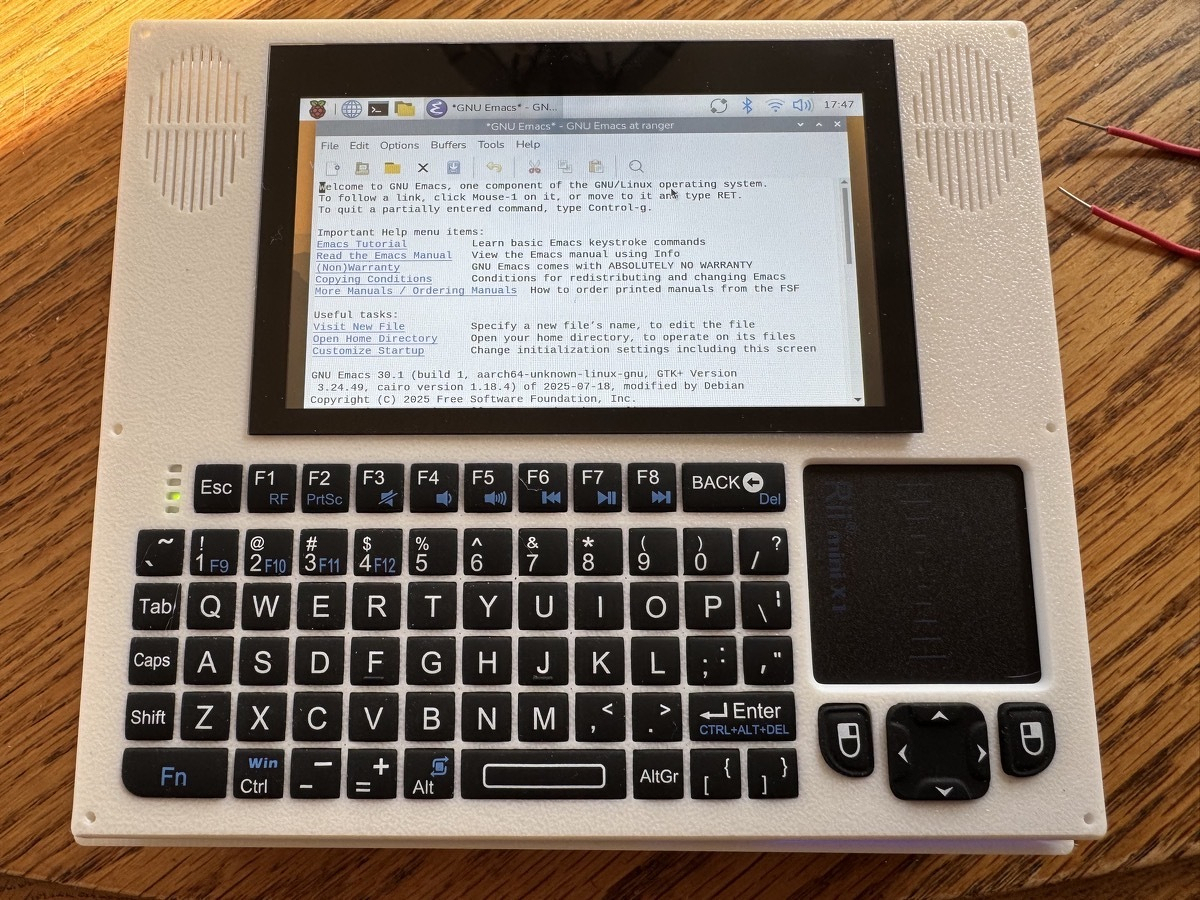
“You wouldn’t download a laptop, would you?”
“I’m saddened that you so completely misunderstand me.”
I have, in fact, downloaded a laptop, printed it, and installed a Free operating system.
In Argentina, U.S. Tech Billionaire Peter Thiel Finds An Escape - The New York Times
In Argentina, U.S. Tech Billionaire Peter Thiel Finds An Escape - The New York Times:
The billionaire’s new roots in Argentina are said to be partly motivated by concerns about the future of the United States and shared beliefs with Argentina’s right-wing leader.
Don’t let the proles hit you on the ass on the way out, just kidding, let them for all I care.
I’m going to use jj instead of git for the next 2 weeks. Hold me to this.
Today’s agenda:
5:15AM: Up for a video call with Eastern Europe. (Context: I’m in California.)
7AM: Commuting to work.
4PM: Leaving work.
5PM: Meeting up with the backpack cult for a 5 mile weight-carrying hike around the Golden Gate Park and beaches a bridge area.
8PM: Commuting home.
9PM: Animal Crossing until I fall asleep harvesting coconuts.